Keeper Password Manager
For good reason, part of Keeper’s solid reputation as a password manager is thanks to its standout security and encryption methods. Keeper uses a zero-knowledge system that, by encrypting and decrypting information on users’ devices, means the company never has access to or knowledge of users’ passwords. . Keeper is the world’s most trusted and downloaded password manager with a 4.9 rating from over 100,000 reviews. Millions of people and thousands of businesses trust Keeper. No limit to the number of passwords you can store.
-->The objective of this tutorial is to demonstrate the steps to be performed in Keeper Password Manager & Digital Vault and Azure Active Directory (Azure AD) to configure Azure AD to automatically provision and de-provision users and/or groups to Keeper Password Manager & Digital Vault.
Note
This tutorial describes a connector built on top of the Azure AD User Provisioning Service. For important details on what this service does, how it works, and frequently asked questions, see Automate user provisioning and deprovisioning to SaaS applications with Azure Active Directory.
This connector is currently in Public Preview. For more information on the general Microsoft Azure terms of use for Preview features, see Supplemental Terms of Use for Microsoft Azure Previews.
Prerequisites
The scenario outlined in this tutorial assumes that you already have the following prerequisites:
- An Azure AD tenant
- A user account in Keeper Password Manager & Digital Vault with Admin permissions.
Add Keeper Password Manager & Digital Vault from the gallery
Before configuring Keeper Password Manager & Digital Vault for automatic user provisioning with Azure AD, you need to add Keeper Password Manager & Digital Vault from the Azure AD application gallery to your list of managed SaaS applications.
To add Keeper Password Manager & Digital Vault from the Azure AD application gallery, perform the following steps:
In the Azure portal, in the left navigation panel, select Azure Active Directory.
Go to Enterprise applications, and then select All applications.
To add a new application, select the New application button at the top of the pane.
In the search box, enter Keeper Password Manager & Digital Vault, select Keeper Password Manager & Digital Vault in the results panel, and then click the Add button to add the application.
Assigning users to Keeper Password Manager & Digital Vault
Azure Active Directory uses a concept called assignments to determine which users should receive access to selected apps. In the context of automatic user provisioning, only the users and/or groups that have been assigned to an application in Azure AD are synchronized.
Before configuring and enabling automatic user provisioning, you should decide which users and/or groups in Azure AD need access to Keeper Password Manager & Digital Vault. Once decided, you can assign these users and/or groups to Keeper Password Manager & Digital Vault by following the instructions here:
Important tips for assigning users to Keeper Password Manager & Digital Vault
It is recommended that a single Azure AD user is assigned to Keeper Password Manager & Digital Vault to test the automatic user provisioning configuration. Additional users and/or groups may be assigned later.
When assigning a user to Keeper Password Manager & Digital Vault, you must select any valid application-specific role (if available) in the assignment dialog. Users with the Default Access role are excluded from provisioning.
Configuring automatic user provisioning to Keeper Password Manager & Digital Vault
This section guides you through the steps to configure the Azure AD provisioning service to create, update, and disable users and/or groups in Keeper Password Manager & Digital Vault based on user and/or group assignments in Azure AD.
Tip
You may also choose to enable SAML-based single sign-on for Keeper Password Manager & Digital Vault, following the instructions provided in the Keeper Password Manager & Digital Vault single sign-on tutorial. Single sign-on can be configured independently of automatic user provisioning, though these two features compliment each other.
To configure automatic user provisioning for Keeper Password Manager & Digital Vault in Azure AD:
Sign in to the Azure portal. Select Enterprise Applications, then select All applications.
In the applications list, select Keeper Password Manager & Digital Vault.
Select the Provisioning tab.
Set the Provisioning Mode to Automatic.
Under the Admin Credentials section, input the Tenant URL and Secret Token of your Keeper Password Manager & Digital Vault's account as described in Step 6.
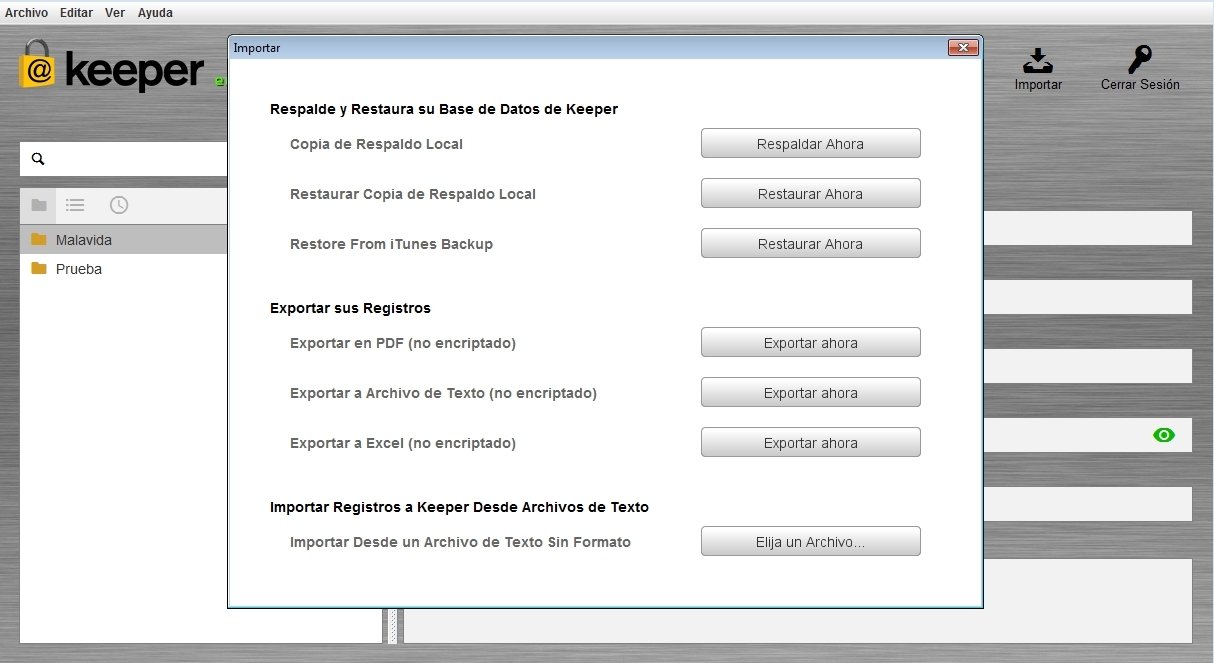
Sign in to your Keeper Admin Console. Click on Admin and select an existing node or create a new one. Navigate to the Provisioning tab and select Add Method.
Select SCIM (System for Cross-Domain Identity Management.
Click Create Provisioning Token.
Copy the values for URL and Token and paste them into Tenant URL and Secret Token in Azure AD. Click Save to complete the provisioning setup on Keeper.
Upon populating the fields shown in Step 5, click Test Connection to ensure Azure AD can connect to Keeper Password Manager & Digital Vault. If the connection fails, ensure your Keeper Password Manager & Digital Vault account has Admin permissions and try again.
In the Notification Email field, enter the email address of a person or group who should receive the provisioning error notifications and check the checkbox - Send an email notification when a failure occurs.
Click Save.
Under the Mappings section, select Synchronize Azure Active Directory Users to Keeper Password Manager & Digital Vault.
Review the user attributes that are synchronized from Azure AD to Keeper Password Manager & Digital Vault in the Attribute Mapping section. The attributes selected as Matching properties are used to match the user accounts in Keeper Password Manager & Digital Vault for update operations. Select the Save button to commit any changes.
Under the Mappings section, select Synchronize Azure Active Directory Groups to Keeper Password Manager & Digital Vault.
Review the group attributes that are synchronized from Azure AD to Keeper Password Manager & Digital Vault in the Attribute Mapping section. The attributes selected as Matching properties are used to match the groups in Keeper Password Manager & Digital Vault for update operations. Select the Save button to commit any changes.
To configure scoping filters, refer to the following instructions provided in the Scoping filter tutorial.
To enable the Azure AD provisioning service for Keeper Password Manager & Digital Vault, change the Provisioning Status to On in the Settings section.
Define the users and/or groups that you would like to provision to Keeper Password Manager & Digital Vault by choosing the desired values in Scope in the Settings section.
When you are ready to provision, click Save.
This operation starts the initial synchronization of all users and/or groups defined in Scope in the Settings section. The initial sync takes longer to perform than subsequent syncs, which occur approximately every 40 minutes as long as the Azure AD provisioning service is running. You can use the Synchronization Details section to monitor progress and follow links to provisioning activity report, which describes all actions performed by the Azure AD provisioning service on Keeper Password Manager & Digital Vault.
For more information on how to read the Azure AD provisioning logs, see Reporting on automatic user account provisioning.
Connector Limitations
- Keeper Password Manager & Digital Vault requires emails and userName to have the same source value, as any updates to either attributes will modify the other value.
- Keeper Password Manager & Digital Vault does not support user deletes, only disable. Disabled users will appear as locked in the Keeper Admin Console UI.
Additional resources
Next steps
Of the many ‘silver bullets’ out there looking to finally slay the password, none have been able to succeed. What this means is that passwords are here to stay, at least for the time being, and your best shot at both generating unique and cryptographically secure passwords and retrieving them whenever they’re needed is with a password manager.
This is what security experts have been advocating for years because these tools create a safe environment in which users can store all of their credentials and financial data without the hassle of remembering each and every username and password. But how do you pick the best password management service?
One of the key pieces of advice that security experts (ourselves included) give is to take a look at whether the password management service has been hacked before or not, as well as whether it ‘features’ any security vulnerabilities that white-hat hackers have shared with the service providers. If the password management service has patched any vulnerabilities, then it could be a good choice.
Use our special promotional code below and if you haven’t used RoboForm before you can enjoy RoboForm Everywhere or Family for as low as $1.16 per month, saving 30% on the subscription fees.
To help make that decision a little easier, let's take a look at the hacking history of some password managers. The aim isn’t a complete list, as you'll see, but we have instead explored the most important hacks and the security vulnerabilities over years.
2014
- LastPass, My1Login, NeedMyPassword, PasswordBox, and RoboForm: Researchers at the University of California Berkeley discovered a number of vulnerabilities in a handful of password managers. “In four out of the five password managers we studied, an attacker can learn a user's credentials for arbitrary websites,” researchers Zhiwei Li, Warren He, Devdatta Akhawe, and Dawn Song wrote in their paper.
- RoboForm: IT security consultant and tech enthusiast Paul Moore discovered one critical vulnerability in and a privacy loophole in the password management service that could allow attackers and prying eyes to obtain users' personal data, including stored login credentials of various websites and even card payment details.
2015

- KeePass: When this program runs on a computer where a logged in user has the KeePass database unlocked, KeeFarce (a hacking tool)decrypts the entire database and writes it to a file that the hacker can easily access. In theory this kind of hack makes all password managers vulnerable.
- LastPass: An intrusion to the company’s servers was detected. While encrypted user data wasn't stolen, cyber criminals stole LastPass account email addresses, password reminders, server per-user salts, and authentication hashes.
2016
- MyPasswords, Informaticore, LastPass, Keeper, F-Secure Key, Dashlane, Keepsafe, Avast Passwords, and 1Password: This was a busy year in terms of password management vulnerabilities. TeamSIK (Security Is Key), a group of people interested in IT security from the Fraunhofer Institute for Secure Information Technology, discovered serious security flaws in the most popular password management apps developed for the Android platform.
- LastPass: Google Project Zero Hacker Tavis Ormandy discovered a critical zero-day flaw that allowed any remote attacker to compromise accounts completely.

2017
- LastPass: Tavis Ormandy discovered a vulnerability in its browser plugins, which LastPass called a “major architectural problem“. The password management service advised users to avoid using its browser plugins while it dealt with the issue.
- OneLogin: An attacker had “obtained access to a set of AWS keys and used them to access the AWS API from an intermediate host with another, smaller service provider in the U.S.”
- Keeper: Tavis Ormandy discovered that the service was exposing passwords to unreliable web pages.
Does This Mean We Should Stop Using Password Managers?
No, not at all. The recent hacks and security vulnerabilities found in these services underscore one important aspect in security: no piece of software is able to truly offer more than 99% security. Reaching 100% security is impossible with any kind of software because every piece of code will have an Achilles heel somewhere that makes it vulnerable.
The question is different in this case: what does the team of developers do to protect user data, and what attack scenarios did they have in mind when they coded the software? Of course, if a service is static and the developers don't keep their security up to date, then it can easily be hacked.
How user data is protected should be the main consideration when picking a password manager. Other features have their importance, but this is something you should always consider before making the final decision. For example, how do the developers communicate the bad news to their users? Transparency in communication is also another important aspect.
Free password managers are great utilities to start with, just be sure to keep an eye on the updates. Check the update history of the software and if there isn’t much to check on, then it can be considered a sign to move on to the next one. A lot can happen in just a few weeks in the security industry, so the bare minimum on your list of expectations should be up-to-date software and a quick response time to any security breaches or attacks. Otherwise, you could end up vulnerable to cyber attacks, which isn’t the opposite of what you wanted in the first place.
Best Password Managers of 2021
Edge Password Manager
| Rank | Provider | Info | Visit |
| Editor's Choice 2021 |
| ||
| |||
|
Keeper Password Manager
More FAQs
